2022 Prospective Student Visit Day and Graduate Research Symposium

The Computer Science (CS) department welcomes prospective students interested in our graduate programs to our annual Prospective Student Visit Day on Friday, Nov. 4. We are looking for strong students with diverse backgrounds to join our MCS and PhD programs. A wide variety of research areas is represented by our world-class faculty including algorithms, computational epidemiology, distributed computing, human-computer interaction, machine learning, massive data algorithms and technology, mobile computing, networks, programming languages, text mining, security, and virtual reality. Write to our Graduate Program Administrator at cs-info@list.uiowa.edu if you'd like to visit.
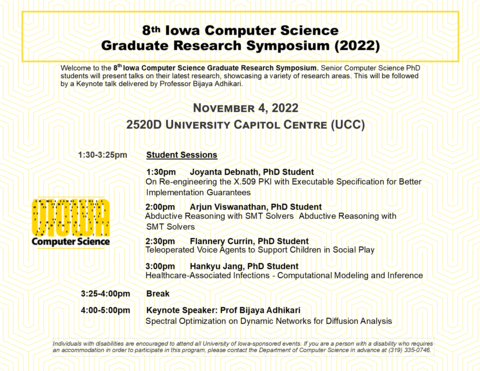
An important part of the prospective Student Visit Day is the 8th Iowa Computer Science Graduate Research Symposium (2022), in which senior PhD students will present talks showcasing their current research. This will be followed by a keynote by a CS faculty member. Talks are intended for a wide audience with interest in CS, including CS juniors and seniors. The talks presented by current CS graduate students at the Symposium are excellent examples of the exciting CS research taking place here on the UI campus!
Schedule
All times CT [Conversion to your timezone possible here if needed]
Friday, Nov. 4, 2022 |
Morning Session (By invitation) |
|
Morning |
Overview of Graduate Programs by Professor and Director of Graduate Studies Kasturi VaradarajanShort Faculty Research Presentations by Professors Garrett Morris, Sriram Pemmaraju, and Supreeth Shastri |
|
Graduate Student Research Symposium Sessions |
||
1:30-3:25 p.m. |
Student Sessions |
|
|
1:30 p.m. |
Joyanta Debnath, PhD Student On Re-engineering the X.509 PKI with Executable Specification for Better Implementation Guarantees. |
|
|
2 p.m. |
Arjun Viswanathan, PhD Student Abductive Reasoning with SMT Solvers |
|
|
2:30 p.m. |
Flannery Currin, PhD Student Teleoperated Voice Agents to Support Children in Social Play |
|
|
3 p.m. |
Hankyu Jang, PhD Student Healthcare-Associated Infections - Computational Modeling and Inference |
|
3:25-4 p.m. |
Break |
|
4-5 p.m. |
Keynote |
|
|
Speaker: Professor Bijaya Adhikari Spectral Optimization on Dynamic Networks for Diffusion Analysis |
||
Speakers
Joyanta Debnath
Title: On Re-engineering the X.509 PKI with Executable Specification for Better Implementation Guarantees
Abstract:
The X.509 Public-Key Infrastructure (PKI) standard is widely used as a scalable and flexible authentication mechanism. Flaws in X.509 implementations can make relying applications susceptible to impersonation attacks or interoperability issues. In practice, many libraries implementing X.509 have been shown to suffer from flaws that are due to noncompliance with the standard. Developing a compliant implementation is especially hindered by the design complexity, ambiguities, or under-specifications in the standard written in natural languages. Therefore, we set out to alleviate this unsatisfactory state of affairs by re-engineering and formalizing a widely used fragment of the X.509 standard specification, and then using it to develop a high-assurance implementation. Our X.509 specification re-engineering effort is guided by the principle of decoupling the syntactic requirements from the semantic requirements. For formalizing the syntactic requirements of X.509 standard, we observe that a restricted fragment of attribute grammar is sufficient. In contrast, for precisely capturing the semantic requirements imposed on the most-widely used X.509 features, we use quantifier-free first-order logic (QFFOL). Interestingly, using QFFOL results in an executable specification that can be efficiently enforced by an SMT solver. We use these and other insights to develop a high-assurance X.509 implementation named CERES. A comparison of CERES with 3 mainstream libraries (i.e., mbedTLS, OpenSSL, and GnuTLS) based on 2 million real certificate chains and 2 million synthetic certificate chains shows that CERES rightfully rejects malformed and invalid certificates.
4th year PhD student | Advisor: Omar Chowdhury | Areas of research: Software Security, Network Security, Automated Reasoning
Arjun Viswanathan
Title: Abductive Reasoning with SMT Solvers
Abstract:
SMT (satisfiability modulo theories) solvers are a class of automatic theorem provers that are used in various applications such as software and hardware verification, program synthesis and symbolic execution. Typically, they perform deductive proofs of logical formulas - a proof of some goal G from hypotheses H1, H2, …, Hn. This talk will focus on the capabilities of the cvc5 SMT solver to perform abductive reasoning for proof completion. Given a goal G that does not follow from hypotheses H1, H2, …, Hn, abduction is the process that finds some additional hypothesis A (an abduct), such that G can be proved from H1, H2, …, Hn, A. We will look at an application of cvc5’s abductive reasoning in the symbolic execution engine Crux, where the user can ask for abducts of failed proof attempts in addition to counterexamples.
6th year PhD student | Advisor: Cesare Tinelli | Area of research: Formal Methods
Flannery Currin
Title: Teleoperated Voice Agents to Support Children in Social Play
Abstract:
Touch screen devices allow children to use technology at younger ages than was previously possible. Children increasingly use technology for entertainment and educational purposes. Adults, especially parents, moderate children's technology use by deciding which devices and software to purchase, setting time limits or restrictions on content, and using parental control apps. Therefore, we must consider parents' attitudes toward technology when designing technology for children. In this presentation, I will outline a Q-Sort approach to constructing parent user profiles and describe three parent profiles constructed using this method. Based on parents' concerns and prior research, I will explain why teleoperated, as opposed to automated, voice agents are more appropriate in certain contexts, and describe two use cases for teleoperated voice agents in supporting children's play.
4th Year PhD student | Advisor: Juan Pablo Hourcade | Areas of research: HCI, child-computer interaction, usability, play, voice agents, and educational technologies
Hankyu Jang
Title: Healthcare-Associated Infections - Computational Modeling and Inference
Abstract:
Each year, roughly 4% of patients in the U.S. are diagnosed with infection during their care in the hospital. These health care-associated infections (HAIs) are a threat to patient health. Therefore, hospitals, clinics, and long-term care facilities are interested in preventing and mitigating the spread of HAIs. However, designing an efficient intervention strategy is challenging due to the complex dynamics of disease. Also, the observed infections may be the tip of the iceberg in the midst of latent spreaders. This talk gives a high-level overview of the methods we proposed in recent years to solve problems in computational modeling and inference of HAIs. Specifically, we discuss the disease models and the corresponding nonpharmaceutical interventions (NPIs) for HAIs that we designed to reduce the spread of infections in the hospital. Furthermore, we discuss our methods for detecting asymptomatic infections and infection sources. Finally, we show our method of learning the representation of patients over time from their electronic health records (EHR) and that learned embeddings are meaningful in detecting HAIs.
5th year PhD student | Advisors: Alberto Segre, Sriram Pemmaraju | Areas of research: Computational Epidemiology, Graph Mining, Network Embedding
 Keynote Speaker Bijaya Adhikari
Keynote Speaker Bijaya Adhikari

Title: Spectral Optimization on Dynamic Networks for Diffusion Analysis
Abstract:
Whom should we vaccinate in a large population contact network to mitigate an epidemic outbreak? Which places should one avoid visiting to save themself from potential infections? How to compute who gets infected in a large network as quickly as possible? These are important questions in epidemiology and public health. Epidemic outbreaks are often modeled as diffusion processes over underlying contact networks. The large size and the dynamic nature of real-world contact networks make the analysis of the diffusion process, and thus answering the questions above, a major challenge. In this talk, we explore provably near-optimal approaches which leverage the spectral radius of contact networks to facilitate diffusion analysis. The first half of the talk will focus on generating smaller representation of a large contact network to speed up existing techniques and the second half will focus on directly answering questions related to vaccination and quarantining in people-location networks.
Bio: Bijaya Adhikari is an Assistant Professor in the department of Computer Science at the University of Iowa. He received PhD and master's degree in computer science from Virginia Tech and bachelor's degree from Vistula University in Warsaw, Poland. He works at the intersection of epidemiology and AI/ML. His research focuses on building new algorithms and deep learning architectures incorporating epidemiological domain knowledge to solve challenging problems in the real world. He has published at both top data mining and domain-specific venues (SIGKDD, ICDM, WWW, SDM, AAAI, AAMAS, PNAS, PLoS Computational Biology, PNAS etc). His work in epidemic forecasting has won multiple awards. He is also a member of the interdisciplinary Computational Epidemiology group at the University of Iowa.
Individuals with disabilities are encouraged to attend all University of Iowa–sponsored events. If you are a person with a disability who requires a reasonable accommodation in order to participate in this program, please contact Alli Rockwell in advance at (319)384-3621 or allison-rockwell@uiowa.edu



